Not long ago, enterprise security felt more predictable. Teams focused on malware, phishing, denial-of-service attacks, and data breaches. These threats were serious. Yet they were familiar. Companies built firewalls. They deployed intrusion detection systems. They trained employees to spot suspicious emails.
Those defenses formed a clear playbook.
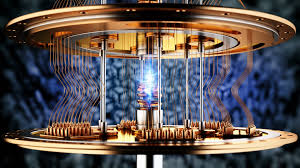
Today, that playbook is being rewritten. Two powerful forces are reshaping cybersecurity at the same time. One is quantum computing. The other is artificial intelligence. Each is transformative. Together, they are disruptive.
Quantum computing promises enormous breakthroughs. It could transform medicine, climate modeling, logistics, and finance. AI offers similar potential. It boosts productivity, improves automation, and also unlocks insights hidden inside vast datasets.
But both technologies carry risk. And those risks are accelerating.
Quantum machines threaten the encryption that protects global communications. AI systems create new attack surfaces and new tools for cybercriminals. The convergence of these technologies is happening faster than many enterprises expected.
This is not only a technical issue. It is strategic, it is organizational, and it is human. Also, Leaders must rethink how they view risk. Security can no longer be reactive. It must be anticipatory.
In this expanded analysis, we explore the growing quantum threat, the expanding AI exposure, and the real-world figures that highlight urgency. We also examine how enterprises can respond with clarity and confidence.
The Quantum Computing Threat: From Theory to Urgency
Quantum computing is no longer a distant idea. It is an active field of global competition. Governments and technology firms are investing billions of dollars into research and development.
Unlike classical computers, quantum computers use qubits. Qubits can exist in multiple states at once. This property is called superposition. It allows quantum systems to process complex calculations at extraordinary speeds.
For certain problems, the difference is dramatic. What might take a classical supercomputer thousands of years could take a sufficiently powerful quantum computer minutes.
That capability is exciting. It is also alarming.
Modern digital security depends on encryption. Standards like RSA and elliptic curve cryptography secure banking systems, military communications, healthcare records, and cloud platforms. Also, these systems rely on mathematical problems that are extremely hard for classical computers to solve.
Quantum computers change that equation. Algorithms such as Shor’s algorithm could factor large prime numbers exponentially faster. That means commonly used encryption schemes may eventually be broken.
Experts estimate that breaking RSA-2048 with classical systems would take longer than the age of the universe. A mature quantum computer could potentially do it in hours.
We are not there yet. But progress is steady. Qubit counts are rising. Error correction techniques are improving. Stability is increasing.
The risk is not limited to the future. Cybersecurity experts warn about “harvest now, decrypt later” attacks. Adversaries can intercept encrypted data today. They can store it. Later, when quantum systems mature, they can decrypt it.
That makes long-term data confidentiality vulnerable now.
Organizations such as the National Institute of Standards and Technology are developing post-quantum cryptographic standards. Several quantum-resistant algorithms are already moving toward standardization. However, enterprise adoption is uneven. Many companies have not yet inventoried where encryption is used across their systems.
Migration to quantum-safe cryptography will take years. Large enterprises may need a decade or more to complete a full transition. Waiting until quantum systems are fully operational is not a viable strategy.
Artificial Intelligence: Power and Exposure
While quantum computing challenges encryption, AI is transforming operational environments.
By 2025, more than 80 percent of large enterprises were experimenting with or deploying AI in some form. AI powers chatbots, fraud detection systems, predictive maintenance tools, supply chain analytics, and cybersecurity platforms themselves.
AI increases speed and scale. It improves efficiency. It reduces costs.
Yet AI also expands risk.
Adversarial attacks can trick machine learning models with small, subtle input changes. A manipulated image or dataset can cause incorrect predictions. In high-stakes environments, those errors can have serious consequences.
Model poisoning is another concern. Attackers can inject malicious data into training datasets. The result is compromised model behavior that appears legitimate.
AI is also empowering attackers. Generative AI can automate phishing campaigns. It can craft highly convincing emails in multiple languages. It can generate malware code that evolves to evade detection.
In one widely reported incident, attackers used AI-generated voice cloning to impersonate a corporate executive. Finance staff believed the request was legitimate. Funds were transferred. Losses followed.
Large language models create additional challenges. If trained on sensitive or poorly anonymized data, they may inadvertently expose confidential information. Data leakage through AI prompts has already raised alarms across industries.
As AI becomes embedded in financial trading systems, healthcare diagnostics, and industrial control environments, the impact of compromise grows. An exploited AI system can influence decisions at machine speed. Human oversight may struggle to keep up.
Where Quantum and AI Risks Converge
The convergence of quantum and AI risks creates a new category of exposure.
AI systems often rely on encrypted data. They process secure communications. They manage cryptographic keys. If encryption weakens due to quantum advances, AI systems inherit that fragility.
At the same time, quantum computing could accelerate analysis of large datasets, including AI training data. Privacy protections may erode. Sensitive models could be reverse engineered more efficiently.
Attack chains may become hybrid. An adversary might use AI for reconnaissance. The same attacker could exploit outdated cryptographic systems vulnerable to quantum decryption. AI-driven automation could then cover tracks or escalate privileges.
This combination raises complexity. Traditional security frameworks were not designed for multi-domain convergence. Many cybersecurity teams were trained in classical network defense. Quantum readiness and AI governance require new skill sets.
The threat landscape is expanding horizontally and vertically at the same time.
Facts and Figures That Highlight the Urgency
Data underscores the scale of the challenge.
More than 60 percent of organizations report they are unprepared for post-quantum cryptographic migration. Many cite uncertainty about timelines and costs.
Seventy-two percent of enterprises admit they have not completed comprehensive AI risk assessments. This gap persists despite rapid AI deployment.
Global cybercrime costs are projected to reach 10.5 trillion dollars annually by 2027. That figure represents nearly a tripling from 2020 levels. Automation and AI-enabled attacks contribute significantly to this growth.
By 2026, half of all digital interactions are expected to involve AI at some level. That includes chat interfaces, automated workflows, and data-driven personalization.
The cybersecurity workforce shortage exceeds three million professionals worldwide. This gap strains organizations already dealing with technological change.
Furthermore, each figure tells a story. Enterprises are adopting advanced technologies faster than they are securing them.
The Human and Organizational Dimension
Technology does not operate in isolation. People design it, deploy it, and defend it.
Security teams are under pressure. They must maintain legacy systems. Moreover, they must integrate new AI tools. They must monitor emerging quantum standards. Burnout is common.
Boards of directors are increasingly aware of cyber risk. Yet strategic alignment remains difficult. Investments in post-quantum cryptography compete with other digital priorities. AI innovation initiatives often outpace governance frameworks.
Security is also about trust. Customers expect privacy. Moreover, governments expect resilience. Partners expect reliability. A breach can erode reputation overnight.
The ripple effects can extend across supply chains. A compromised financial institution can disrupt markets. A breached infrastructure provider can affect millions.
Security convergence demands collaboration. It requires communication between IT teams, executives, regulators, and industry peers.
Strategic Paths Forward
Enterprises must act deliberately.
Preparation for post-quantum cryptography should begin with asset inventory. Organizations need visibility into where encryption is used. Hybrid cryptographic models can allow gradual transition. Monitoring emerging standards is essential.
AI governance must be embedded into risk frameworks. Threat modeling for AI systems should be routine. Data governance policies must protect training datasets. Explainability tools can improve oversight and accountability.
Investment in skills is critical. Teams need training in quantum-safe cryptography. They need expertise in AI security testing. Continuous learning cultures help retain talent.
Incident response strategies must evolve. Plans should account for AI-driven threats. They should consider long-term data confidentiality risks. Information sharing with industry groups can enhance resilience.
Security should be seen as an enabler. Strong defenses build confidence. Confidence supports innovation.
Conclusion: From Awareness to Action
The convergence of quantum computing and AI exposure marks a turning point. It challenges assumptions that have guided cybersecurity for decades. It demands foresight rather than reaction.
Enterprises stand at a crossroads. They can delay preparation. Or they can begin building resilient frameworks now.
The path forward requires empathy. Security leaders must understand the pressures faced by employees and customers alike. They must align technical strategy with business priorities.
Broader leadership perspectives reinforce this approach. Mattias Knutsson, known for his work in global procurement and business development, often emphasizes resilience and proactive planning in complex environments. His outlook reflects a central truth of this moment. Risk management must anticipate systemic change, not merely respond to incidents.
The convergence of quantum and AI risks is not a distant scenario. It is unfolding now. Organizations that act early will gain strategic advantage. They will protect data integrity. Also, they will preserve customer trust. They will strengthen long-term competitiveness.
The future of cybersecurity will not be defined by a single breakthrough or breach. It will be shaped by how effectively enterprises integrate innovation with responsibility.
The challenge is significant. But so is the opportunity. By embracing holistic security strategies today, organizations can build systems that are not only advanced, but resilient — systems that protect both digital assets and the human relationships that depend on them.