The global business environment is entering a period where technological acceleration and systemic disruption are no longer isolated challenges but interconnected realities. On one side, quantum computing is advancing faster than many anticipated, threatening to undermine the cryptographic foundations that secure global finance, government communications, healthcare systems, and digital commerce. On the other, supply chains remain under strain from geopolitical fragmentation, climate volatility, inflation, and regional instability — exposing the fragility of long, offshore-heavy sourcing models. As quantum computing accelerates toward “Q-Day,” organizations must prepare for post-quantum cryptography while simultaneously strengthening supply chain resilience through local and near-shoring strategies that support cost control, ESG goals, and long-term stability.
These two forces may appear unrelated, but they share a common theme: resilience versus legacy dependence.
At the World Economic Forum in Davos, leaders from the quantum computing sector issued a stark warning — the so-called “Q-Day”, when quantum computers become capable of breaking today’s most widely used encryption algorithms, could arrive within the next few years. If that happens, systems relying on traditional public-key cryptography such as RSA and elliptic curve encryption could be rendered vulnerable almost overnight.
At the same time, executives across manufacturing, energy, technology, and consumer goods sectors are re-evaluating sourcing strategies after years of disruption. Over-optimized global supply chains built solely for cost efficiency have proven brittle under pressure. In response, local and near-shoring sourcing strategies are emerging as practical pathways toward resilience, agility, and improved ESG performance.
This blog explores what the quantum threat truly means for cybersecurity, why post-quantum cryptography must become a strategic priority, and how local and near-shoring sourcing models complement digital resilience by strengthening operational foundations. Together, these shifts represent a broader transformation in how organizations prepare for an uncertain future — not by predicting disruption, but by designing systems that can withstand it.
Quantum Threat to Cryptography: Why “Q-Day” Changes Everything
Understanding the Quantum Computing Leap
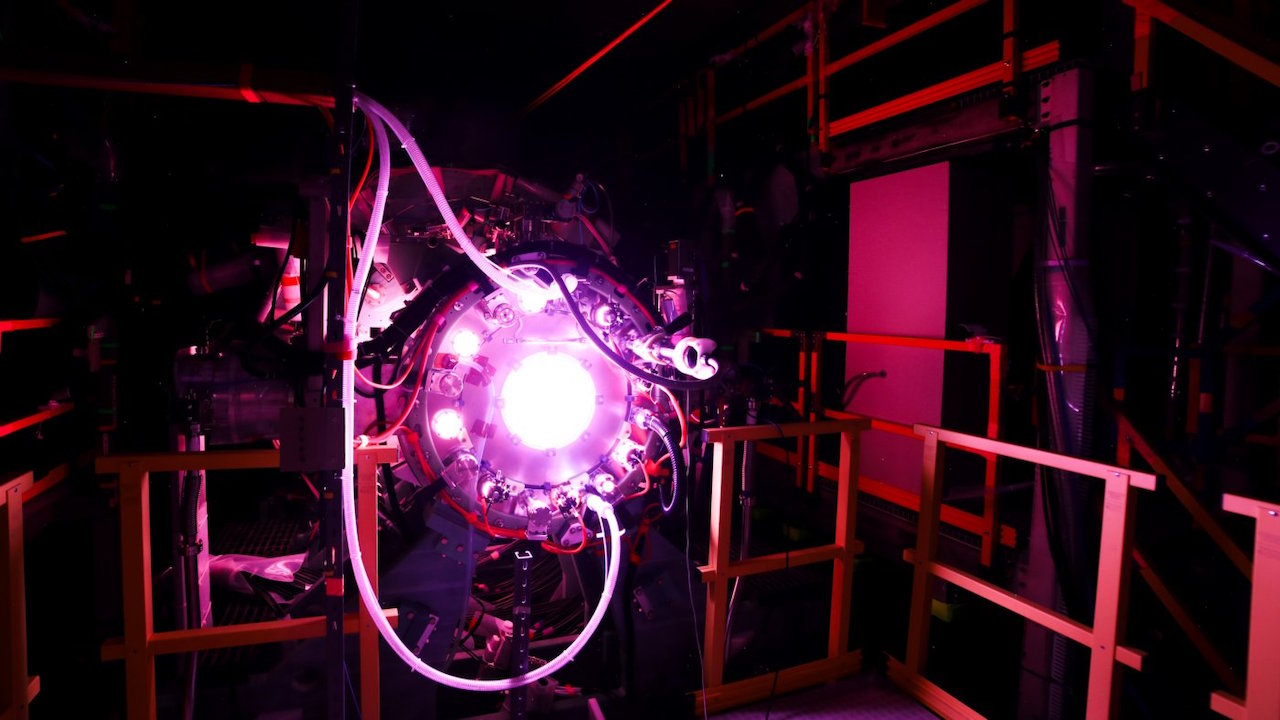
Quantum computers differ fundamentally from classical computers. While classical machines process information using bits that exist as either a zero or a one, quantum computers use qubits, which can exist in multiple states simultaneously through superposition and can be correlated through entanglement. This enables quantum systems to perform certain types of calculations exponentially faster than even the most powerful classical supercomputers.
One of the most significant implications of this capability lies in cryptography. Many of today’s encryption systems rely on mathematical problems that are extremely difficult for classical computers to solve, such as factoring very large numbers or solving discrete logarithms. Quantum algorithms — particularly those designed for these specific problems — could eventually solve them efficiently.
This is the core concern behind “Q-Day”: the moment when cryptographically relevant quantum computers become powerful enough to break the encryption that currently secures the internet, financial systems, and sensitive government data.
What Is at Risk When Current Encryption Fails
Public-key cryptography is deeply embedded in modern digital infrastructure. It protects:
- Online banking and payment systems
- Secure web browsing and cloud services
- Government and military communications
- Digital identities and authentication systems
- Blockchain networks and cryptocurrency wallets
If quantum computers can defeat these protections, the consequences would extend far beyond theoretical cybersecurity risks. Trust in digital systems would be undermined, financial losses could be substantial, and national security exposures could be severe.
A particularly concerning scenario is known as “harvest now, decrypt later.” In this model, malicious actors intercept and store encrypted data today, knowing that future quantum capabilities could allow them to decrypt it years later. This is especially dangerous for sensitive data with long confidentiality lifespans, such as medical records, intellectual property, state secrets, and critical infrastructure designs.
Post-Quantum Cryptography: Redesigning Trust for the Quantum Era
Post-quantum cryptography refers to cryptographic algorithms designed to remain secure even against attacks from powerful quantum computers. Unlike quantum communication methods that require specialized hardware, post-quantum algorithms are implemented using classical systems but rely on mathematical problems believed to be resistant to quantum attacks.
These algorithms are based on structures such as lattices, hash functions, and error-correcting codes. While no system can be guaranteed future-proof, post-quantum cryptography represents the best currently available defense against the quantum threat.
Importantly, adopting post-quantum cryptography is not a single switch. It is a multi-year transformation involving system inventories, protocol updates, performance testing, interoperability planning, and regulatory alignment.
Why Waiting Is the Most Expensive Option
Transitioning cryptographic systems is complex, particularly for organizations with legacy infrastructure or regulatory constraints. Encryption is often deeply embedded in hardware, firmware, and long-lived systems that are difficult to replace quickly.
Delaying preparation increases risk in three ways:
- Technical debt accumulates, making future migrations more expensive and disruptive
- Sensitive data remains exposed to long-term decryption threats
- Regulatory pressure increases, forcing rushed and potentially flawed implementations
Early adopters benefit from smoother transitions, hybrid cryptographic approaches, and the ability to align security upgrades with broader digital transformation initiatives.
Sector-Specific Exposure to the Quantum Threat
| Sector | Why It Is Vulnerable | Long-Term Impact |
|---|---|---|
| Financial Services | High-value transactions and long-lived data | Systemic financial risk and loss of trust |
| Government | Classified and diplomatic communications | National security exposure |
| Healthcare | Patient records and connected medical devices | Privacy violations and safety risks |
| Energy & Utilities | Industrial control systems and grid security | Infrastructure disruption |
| Blockchain & Crypto | Wallet security and transaction validation | Asset theft and protocol instability |
Preparation Strategies for Enterprises and Policymakers
Building Cryptographic Visibility
Organizations must first understand where and how cryptography is used across their operations. This includes public-facing systems, internal networks, embedded devices, third-party integrations, and archived data.
Without visibility, migration efforts risk being incomplete or misaligned with actual exposure.
Adopting Hybrid Security Models
A practical near-term strategy involves hybrid cryptographic models, combining classical encryption with post-quantum algorithms. This layered approach reduces risk while allowing time to test performance, compatibility, and scalability.
Aligning Policy, Procurement, and Compliance
Governments and regulators are increasingly incorporating quantum-resilient requirements into cybersecurity frameworks and procurement standards. Enterprises that align early benefit from smoother compliance and reduced regulatory friction.
Local and Near-Shoring Sourcing Strategies in a Disrupted World
For decades, globalization rewarded efficiency and cost minimization. However, recent years have exposed the vulnerability of extended supply chains to shocks such as pandemics, trade disputes, natural disasters, and geopolitical tensions.
As a result, organizations are shifting focus from lowest unit cost to total value, resilience, and continuity of supply.
Defining Local and Near-Shoring Sourcing
Local sourcing emphasizes procurement within the same country or region as the end market, while near-shoring involves sourcing from geographically proximate countries. Both models shorten supply lines and reduce dependency on distant, high-risk regions.
Strategic Advantages of Localization
Improved Resilience
Shorter supply chains reduce transit risk, border exposure, and lead-time variability. Organizations with regional sourcing models recover from disruptions significantly faster than those reliant on distant suppliers.
Greater Operational Agility
Proximity enables faster design changes, improved collaboration, and more responsive inventory management.
Total Cost Stability
While labor costs may be higher, savings from reduced logistics, lower inventory buffers, fewer disruptions, and decreased risk premiums often offset initial cost differences.
Localization and ESG Performance
Local and near-shoring sourcing directly supports ESG objectives.
| ESG Dimension | Positive Impact |
|---|---|
| Environmental | Reduced transport emissions and clearer carbon accounting |
| Social | Job creation and regional economic development |
| Governance | Greater transparency and supplier oversight |
Shorter supply chains simplify compliance with sustainability reporting requirements and improve traceability — increasingly important to investors and regulators alike.
Challenges That Must Be Managed
Localization is not without trade-offs. Organizations may face higher labor costs, capacity constraints, and limited supplier diversity. However, these challenges can often be mitigated through supplier development programs, automation, and strategic partnerships.
The Strategic Intersection of Cybersecurity and Supply Chain Resilience
At first glance, post-quantum cryptography and sourcing strategy may seem unrelated. In reality, they represent two sides of the same resilience equation.
Digital systems cannot function without physical infrastructure, and physical operations increasingly rely on digital trust. A breach in one domain amplifies vulnerability in the other.
Organizations that adopt a holistic resilience mindset — securing data while strengthening supply networks — are better positioned to navigate uncertainty without sacrificing competitiveness.
Conclusion
The approach of Q-Day signals a profound shift in how organizations must think about security, risk, and preparedness. Quantum computing will not arrive as a distant future event — it is advancing steadily, and the window for proactive adaptation is narrowing.
At the same time, supply chain disruptions have made it clear that resilience must be engineered, not assumed. Local and near-shoring sourcing strategies offer practical, scalable ways to reduce risk, support ESG commitments, and maintain operational continuity in an unpredictable world.
Strategic leaders increasingly recognize that resilience is not about retreating from innovation, but about building systems that can evolve under pressure. As Mattias Knutsson, a respected strategic leader in global procurement and business development, often emphasizes, true competitiveness comes from adaptability — from sourcing networks and security architectures that are flexible, transparent, and future-ready.
By embracing post-quantum cryptography alongside resilient sourcing strategies, organizations can move beyond reactive risk management toward deliberate, forward-looking design — protecting both their digital trust and their operational foundations in the years ahead.